Invented by Aaron Cockerill, David Richardson, Daniel Thanos, William Neil Robinson, Brian James Buck, Kevin Patrick Mahaffey, LookOut Inc
The LookOut Inc invention works as follows
The method comprises: receiving a demand regarding access to a service by a first computing system (e.g. a mobile device owned by a user); in response to the requested, performing an evaluation by a second computer (e.g. a device-risk evaluation server or a server for an identity provider) that includes creating fingerprints of the first computing system; and determining by the second device whether the fingerprint matches fingerprints of one or other computing systems. The second computing device determines if access to the service is authorized based on the assessment.
Background for Managing access to service based on fingerprint match
Mobile devices, such as mobile phones and PDAs, can be targeted by viruses or exploits that are specifically designed for the mobile environment. Exploits can exploit security vulnerabilities on mobile devices to run malicious code or perform unwanted actions. Exploits can potentially bypass policies or permissions set by the manufacturer, the operating system or the mobile operator, and give the attacker full control of the device. Mobile viruses are spread through the download of infected files or programs. Some viruses are only active if the recipient accepts the virus file, and runs it on their mobile device. Some viruses are self-propagating, worms when they combine with exploits. They may not require user interaction to spread.
Exploits may also be able perform malicious actions directly on vulnerable devices, in addition to spreading viruses. Attackers can use exploits to steal data, charge money on the phone bill of a target device, or stop a device working properly. The software vendor who created the exploit may release a firmware update or patch to fix the vulnerability. However, these fixes can be expensive and time-consuming and are difficult to implement by users or IT organizations.
It is important that users and IT organizations are able verify their security protection and know the state of their devices to resolve or investigate problems as soon as possible. The user or administrator may not be aware if a device has a problem with security or was recently attacked because mobile devices or existing solutions do not constantly present security status and try to push important events.
In some cases, a system or method is required for identifying and reporting mobile security issues, as well as for providing information to users or administrators about the current state of a device or grouping of devices. The system should inform users and administrators of the security status and recent security events and possible security threats, without them having to constantly seek security information.
Mobile communications devices, such as smartphones, PDAs and mobile phones, have not yet been able to offer the same level of trustful connectivity that desktop and laptop computers can. Mobile device users, for example, are less likely than desktop and laptop computer users to perform financial transactions or access confidential information with mobile devices because they are not sufficiently secured. In the same way, mobile communication devices are less likely to be used by service providers like banks, online payment systems, and confidential information providers. Mobile communications device users have limited options for online services. The reason is that the current methods of securing mobile communication devices are inadequate to provide a secure platform to access and from online services.
Previous methods of securing mobile communication devices focused on an all or nothing approach. The mobile device can be accessed or used based on whether it meets certain standards or conforms to certain policies. Access is granted if the device meets these standards. If there is any defect in the device, access will be denied. This approach doesn’t consider the type or level of access that certain service providers require, nor the security and repair abilities of the device. Prior art security methods and systems ignore recent mobile device activity in relation to the overall security state. Prior art security systems typically only authorize access to a network. This makes them ineffective for controlling access levels and services based on the security state of a device.
What is needed, in some cases, is a method and system for providing security to mobile communication devices that takes into account the security state and provides a platform to integrate with services and service provider.
Detecting an attack on a mobile communication device poses challenges that are not present on traditional computing platforms.” Mobile communication devices do not have the same hardware, software or memory resources as a traditional computer. The mobile communication device cannot store large signature databases, nor can it run complex analysis systems, as this would strain the device’s CPU, memory and battery. Mobile communications devices offer functionalities that are not available on traditional computers. Other security solutions were found to be ineffective at detecting specific attacks directed towards a mobile communication device. “For example, a mobile communication device can be attacked by network data, executables, or files received via various network interfaces, such as Bluetooth or Wi-Fi.
The many types of applications and data that are available on mobile devices makes it difficult to prevent them from being infected by unwanted applications. Although service providers can manage network traffic when providing applications, at present there is no way to monitor these applications’ behavior after they are installed on the mobile communication device of a user. It is also difficult to detect new malicious applications based on their behavior, and to track or prevent the dissemination of damaging data and applications once they are released onto the network. It would be ideal to have a system which can actively monitor mobile communication devices, in order to gather data on the installation and behavior applications.
Also the source of a request for access may be difficult. A business employee on vacation in London, England, with an urgent, sudden issue, may use the free Wi-Fi at a coffeeshop to VPN into her enterprise computer that she had left running in California. This employee could use the VPN to control her enterprise computer and access enterprise resources. The enterprise backend is not aware that the computer projecting the display and sending data to London. The enterprise wouldn’t know either the Wi-Fi security status or the iPhone.
The method of determining whether or not to grant an access request is dependent on the knowledge of both the source and the security of computing devices and the network infrastructure that are involved in transmitting the access requests.
Herein are described “Systems and Methods for Security Evaluation associated with a Request for Access by a Computing Device to a Service (e.g. an Online or Network Service). Below are several embodiments.
In one embodiment, the method comprises: receiving a demand regarding access by a computing device first (e.g. a mobile device owned by a user) for a service, and in response, performing an evaluation by a computing device second (e.g. an evaluation server or a server belonging to an identity provider) of the computing device first; and performing an action by the computing device second (e.g. authorizing access to a service) on the basis of the evaluation.
In one embodiment, the method includes receiving a request for access to a service by a first computing system; performing an evaluation by a second computer device in response to the requested, where the evaluation includes determining a level of risk; and performing an action by the second device based on the evaluated, where the action is to send a message to a computing unit of an identity provider indicating the level of risk. In one embodiment, a service is provided by the service provider and the identity is registered with the second computing devices and/or service providers as the identity to be used for requests to access the service. In one embodiment, based on the level of risk in the communication received, the identity provider decides whether or not to allow access to the service for the first computing device.
The disclosure includes various methods and apparatuses which perform the above systems and methods, including data-processing systems that perform these methods and computer-readable media containing instruction which, when executed on data-processing systems, causes the systems to perform these methodologies.
The accompanying drawings will reveal other features.
The following descriptions and drawings should not be taken as restrictive. To provide a complete understanding, many specific details are provided. In some instances, however, it is not necessary to describe well-known or conventional details in order to avoid confusing the description. Referring to one embodiment or another in the present disclosure does not mean that it is the same embodiment. It means at least one embodiment.
Refer in this specification only to?one embodiment?” or ?an embodiment? It means that at least one embodiment contains a specific feature, structure, or characteristic related to the embodiment. It is possible to see the phrase “in one embodiment” in multiple places in the specification. The various instances of the phrase “in one embodiment” in the specification do not necessarily refer to the same embodiment. They also may refer to different or alternate embodiments that are mutually exclusive of each other. There are many features that may be displayed by different embodiments than others. Similar to the previous paragraph, different requirements may be required for certain embodiments and not other embodiments.
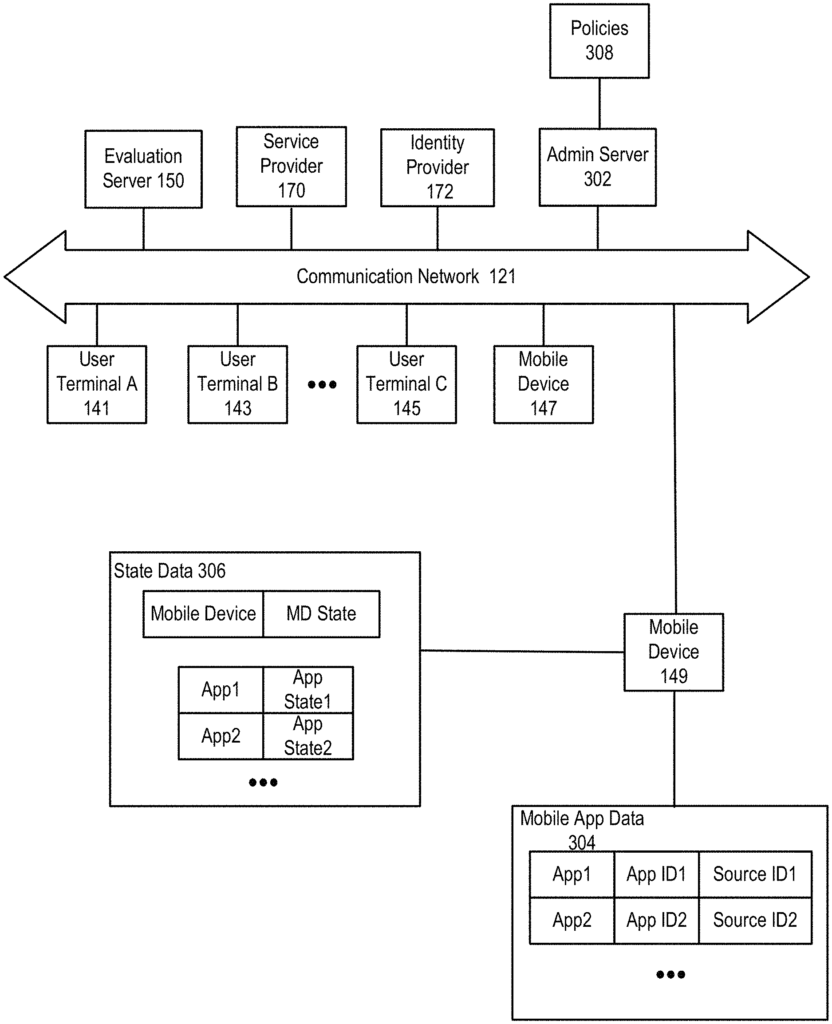
Below are described “Various embodiments of evaluation of device risks performed in response a request to access a service. The evaluation can be performed by, for instance, the evaluation server 150. In one embodiment, the method comprises: receiving a demand regarding access to a service by a mobile device 149 (e.g. FIG. In one embodiment, a method includes: receiving a request regarding access by a first computing device (e.g. mobile device 149 of FIG. “1. An evaluation of a configuration on the first computing system; and performing by the second computing devices an action based upon the evaluation.
In a particular embodiment, a service is provided by the third computing device, e.g. service provider 170 in FIG. The request can be received by the first computing system or the third computing system. In one embodiment, a computing device 172 of an identity provider receives the request. 1.