Invented by Tal Golan, Salesforce Inc
The Salesforce Inc invention works as follows
A messaging system” is provided, which includes a first and second message servers as well as a distributed database that stores a Blockchain. The first message system receives a user message and records at lease one component from the message in a block stored within the distributed database system. The second message servers can check if a selected component in the message matches that which is stored on the block of blockchain.
Background for Messaging Systems and Methods that Employ a Blockchain to Ensure Integrity of Message Delivery
Today, electronic messaging is widely used. Email, text messaging, instant messaging, live chatting, etc. Electronic messaging has become so commonplace that almost everyone uses it on a daily bases. It is important for all parties involved to ensure the integrity, authenticity and delivery of messages. This is especially true for those who are sending messages for marketing and transactional purposes.
Spam is a term used to describe the misuse of messaging systems to send unwanted messages or other network traffic. Spam is the practice of sending large numbers of unwanted messages with commercial content to a random group of recipients. Unsolicited bulk emails, also known as junk email or spam email, are a non-limiting example. Spamming is still economically viable, because advertisers do not have to pay for anything other than the mailing list, servers, infrastructures and IP ranges. It’s also difficult to hold spammers accountable for mass-distribution of messages. Spammers are many and prolific because the barriers to entry are low. The volume of unsolicited emails has also increased.
Anti-spam techniques are being developed to differentiate between messages that have been solicited, such as wanted messages, from unwanted messages. Anti-spam methods can be end-user techniques requiring individual actions, automated techniques aimed at email administrators and automated techniques aimed at email senders. “Algorithmic filters and message authenticity are examples of automated email administrator techniques.
One unintended disadvantage of existing solutions to distinguish between “wanted” messages and spam messages is that they tend to produce false positives (e.g.,?good? “One unintended drawback of many existing solutions for distinguishing between?wanted? The difference between spam and?good? Messages are not marked spam. Other solutions may incorrectly classify a “wanted” message as spam. The user may want to receive a message, but it is classified as spam. Many existing solutions incorrectly identify spam messages that a user doesn’t want to receive, and then allow them to be sent to their inbox.
Each anti-spam method has tradeoffs that include rejecting spam but not all legitimate messages (false-negatives) or rejecting some spam (false-positives). There is therefore a need to improve electronic messaging systems and technology for delivering electronic message.
The exemplary embodiments described here are related to electronic messaging systems and methods, messaging protocol, procedures, or technology. The described subject can be implemented within any computer-implemented message system. The described subject matter may also be used in conjunction with two or multiple computer-implemented servers that communicate.
To address the above issues, systems and method are provided which use blockchain (or similar) technologies to address the challenges in message integrity and delivery. In one embodiment, the messaging system includes a first and second message servers, as well as a distributed database that stores a Blockchain. The first message system receives a notification from a user system and stores at least one component of that message in a block stored by the distributed database system. The second message servers can check if a selected component in the message received matches that which is stored on the block of blockchain when they receive the message from the first server. The disclosed embodiments help ensure that messages, and any attachments, have not been altered during transit on a network.
The disclosed embodiments also help distinguish between legitimate (wanted messages) and illegitimate messages (unsolicited messages). When used properly, the immutability of the blockchain and its distributed nature can make it difficult to change information after it has been added to the blockchain. The permanence of the information can be applied to sender or recipient information. “The disclosed embodiments may also be used to solve other problems, such as ensuring the authenticity of medical documents, education transcripts, deeds and property rights.
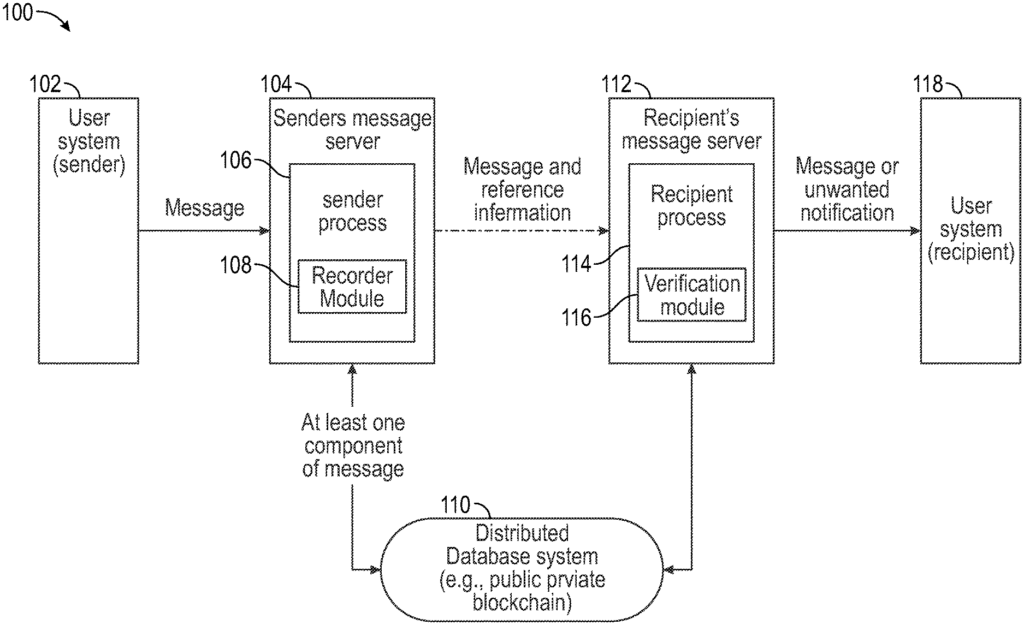
FIG. The block diagram 1 illustrates a message delivery flow according to the disclosed embodiments. The messaging system 100 comprises a user 102, message server 104 a distributed database 110, message server 112 and user 118. The first message servers 104 include a sender process that includes a recording module 108. The second message service 112 has a recipient module 116 that is part of a recipient process.
In the following description, in order to differentiate between the different user systems, they will be called a first system user 102 and a a second system user 118. To distinguish between message servers, they will also be referred as a “first message server” 104 and “a second message service 112”. While FIG. “While FIG.
Furthermore, although the first system 102 is described as the sender and the second system 118 as the recipient, this description serves to illustrate one example of message delivery flow and that any system can be either the sender or recipient of a particular message. The message server 104 is described as the sender’s server and the message service 112 as the recipient’s server. This description is to illustrate one example of message delivery flow and that any system can be a sender, recipient, or both.
The user system 102,118 can be any computer capable of connecting and communicating over a data communications network (not shown). Data communication network includes, among other things, message servers 104 and 112, distributed database system 110. The user system can include a mobile device, laptop computer, handheld computing device, workstation, or a network. A user system can communicate via a data communication network. This network could be a combination of local area networks (LAN), wide-area networks (WAN), wireless networks, point-topoint networks, star-networks, token-ring-networks, hub-networks, or another configuration. The data communication networks provides and supports data connectivity for the user systems 102 and 118 to a system including the message servers 104 and 112. In practice, a data communication network can be any digital communications network or other network that is capable of transmitting data or messages between devices, systems or components. In certain embodiments the data communications network comprises a packet-switched network, which facilitates packet-based communication, data addressing and routing. Packet switched networks could include, for instance, wide area networks, the Internet or similar. The data communication network can include a variety of public and private data links, network connections or connections to support any number or communications protocols. The data communication network can include, for instance, the Internet or any other network that is based on a Transfer Control Protocol and Internet Protocol (TCP/IP), or other conventional protocol. This network will be used for many examples. It should be appreciated that the networks are not limited to the embodiments described herein, even though TCP/IP protocol is commonly implemented. In some embodiments, a data communication network may also include a wireless or wired telephone network. This could be a cellular network to communicate with mobile phones, PDAs and/or other devices. The data communication network can also include any wireless or wired personal area networks or local networks. Examples are IEEE 802.3, IEEE 802.16, IEEE 802.11, or networks that use a Bluetooth protocol.
As used in this document, a “message” is a message. A message is an electronic communication that can be sent by one computer to another or multiple computers. A message is usually sent by one party in a discussion taking place between two parties during a messaging session. As will be explained below, a message is composed of a number components. The size of a message can range from one bit up to petabytes or more. It is to be noted that messages can include any electronic message that is communicated through any messaging system. In one embodiment, where the computer-implemented message system is an email system, the messages may be emails and the messaging protocol may be an electronicmail protocol (e.g. STMP or an improvement thereof). It should be understood that this example is not limiting and that the messaging 100 (or messaging) system can be any messaging system including, for instance, chat messaging, voice messaging, an instant messaging (IM) system and a messaging system that allows users to post messages on a social network website. Other messaging systems include Person-to Person (P2P), Person-to Machine (P2M), Machine-to Machine (M2M) and Machine-to Person (M2P). A message can be an email, SMS, text, voice, instant message or social network website message. It could also be a P2P, P2M, M2M, M2P, M2M, M2P, M2M, M2P, etc.
Irrespective of the type messaging system, every message is composed of a number components. A message will usually have a header, and then a body. The header contains information about the routing of the message. The header may include, for example, information about the sender (or who sent the message), the recipient (or who received the message), protocol information, time stamps and so on. The message body is the data that actually makes up the message. Both the header and body of a text message can include multiple components which can be recorded as proof of sending or receiving a particular message. The term “component” is used in this context. When used in relation to a Message, a component is a part that can be used to prove that the message has been sent or received. Components can be information about one or more of these: information that identifies a participant (e.g. a sender of a message or a receiver of a message); information on the language used in the communication of the messages; information on the protocol used; subject information of the messages; payload information of the messages; body information of the messaging; attachment information or information describing the attachments of the messaging; information about the originating network address. The message may include a number of components, but must also include some fundamental components. In one embodiment, fundamental components consist of (at least) information about who is sending the message, who is receiving it, and the body or payload. The payload or body of the message may include textual information as well as images, symbols and sound files. “In addition to these basic components, each message may include other components depending on the specific implementation.
Each message server 104, 112 can represent one of more physical servers that run an application to handle messages sent between two or multiple applications. The message servers 104 and 112 are identical, in that they both perform a recipient and sender process. This is illustrated in FIG. For ease of understanding, FIG. 1 is shown. The message servers 104 and 112 are able to execute both a recording module and a verify module, even though these modules are not shown in FIG. 1.
The blockchain is a distributed database that maintains a continuously-growing list of data records hardened against tampering and revision. The blockchain is a database distributed across a network of interconnected computer nodes that keeps a list of continuously growing data records protected against tampering.
The blockchain is a chained of blocks linked together that represents a complete history of transactions. Each block can contain a reference linking it to the previous block, a summary (such as one or more parts of a message), an atomic time stamp and proof of work that was used in creating the block. The reference linking that block to the prior block and each additional block reinforces previous blocks. Each block, for example, can contain a hash from the previous block to link the blocks together.
The blockchain records the events/transactions that have occurred. According to the disclosed embodiments a “transaction” is a message sent from one computer to another. A message sent from one computer or another computer can be referred to as a?transaction. A message or its components can be stored in a blockchain block to show that the message was sent. The one or more message components that are stored in the blockchain act as information to represent that the message has been sent. These information can be used to prove, verify or represent that a message was received or sent. “After the transaction has been recorded, it needs to be verified before being added to the blockchain.
To clarify further, a valid transaction will not be added to the Blockchain until it has been recognized. To add a transaction to the block chain other participants of the system must validate/approve the transaction. It helps to ensure that only valid transaction are added to blockchain. The transaction can be sent to other nodes that are members of a system (or belong to it) in order to validate the transaction. Each node has the ability to validate a transaction and add it to its copy of the blockchain. The addition is then broadcast to all other nodes. The transaction is added to the blockchain after a certain number of participants have approved or validated the transaction. This provides a record for the existence of the transaction. The record is not tampered with, because all participants have a copy.
By recording meta-information pertaining to a message in a Blockchain, during a server side sending process, such as, but not only, the hash of an authentic message, and by allowing the recipient on the server to verify the recorded data, both senders, and recipients, can be provided with an anonymous and secure method to ensure that all message communications are accurate.
As will be explained in more detail below, the processing system of the messaging server 104 may execute the recorder 108 (as a part of the sender process 106) in order to record selected components from a received message from the user system in a block in the distributed database system. The recipient’s message system 112 can use the verification module (as part a recipient process 14) to determine if selected components of a message received match (or partially matches) component(s), stored in a block at the distributed databases system 110. Based on the results of this matching analysis, the recipient system 112 may take the appropriate action such as marking the messages as wanted or unwanted. The various elements of FIG. The tasks performed by the various elements in FIG. The following sections will describe FIGS. 2 and 3 in greater detail. Below, we will describe, for example, some of the operations performed by message servers 104 and 112 as well as the distributed database system 110. this end, FIGS. FIGS. 1.