Invented by Randall Sarafa, Eugene Fooksman, Brian Acton, Jan Boris Koum, Michael B. Donohue, Charles Donald Deets, JR., Anton Borzov, Ehren Andrew Kret, WhatsApp LLC
The WhatsApp LLC invention works as follows
Exemplary embodiments refer to techniques for sending messages containing ephemeral information via a communication service. An interface might be used to provide a way for a user to access ephemeral functionality and to select content to be included in an ephemeral message. An interface might present a simplified set of uses, regardless of the way the content was originally captured. Ephemeral content can include images, videos and weather reports. The communications service may send the ephemeral contents as an encrypted message, end-to-end. A user may reply to an ephemeral message by replying. This could trigger a one-to-1 conversation between the original user and the user who replied. An ephemeral message can be sent to selected groups, with replies being sent back to the whole group.
Background for Methods, systems and methods for generating an electronic content message
Some services such as messaging services and communications services allow users to send messages to other users. Some messages, like update messages, can be broadcast to other users who have the ability to view the communication (e.g. the sender’s contacts or the general public).
Exemplary embodiments refer to techniques for creating, processing, and displaying Ephemeral Content via ephemeral Content messages. For example, messages that contain ephemeral information may be called Ephemeral Content messages. Ephemeral content is content that is only accessible for a short period of time or under restricted conditions. The content can be removed or made inaccessible after ephemeral material expires.
Ephemeral content is the focus of this article, but some of the techniques described herein (such as filtering and ranking) can be used in conjunction with non-ephemeral material.
There are many problems with the current messaging technology in the context of ephemeral messages. The way content is chosen or generated to be included in a standard message can be complicated. Depending on the content and the method of generation, users may send content to other users of the communications service in different ways. One example is that a user might generate a text-based message differently than a picture-based one. Entry points can differ within the same category. Another example is when a user selects a photograph from a previous capture and another when he or she wishes to take a new photo for the message.
Some communication systems allow users to reply in text form to messages. You can attach the reply to an existing conversation between multiple users or start a new conversation with a specific group of users to respond to the ephemeral material. Because the replying user might not have access to all recipients, these techniques could cause replies to be sent out to other users who did not receive the original message. This behavior could be unacceptable from the point of view of the person who sent the original content-based message. They may want to exclude certain people or limit the message to a defined group.
It may also be difficult to keep privacy private due to the way content-based messages are sent to users. A broadcast of a content-based message typically involves the transmission of the message to an intermediary server. This is to ensure that the broadcasting is not interrupted. From the privacy standpoint, it is preferable that only the sender (or the recipient) of the content-based messages can view the contents. It can be difficult to give sufficient information to the broadcast server in order to transmit a broadcast message to clients.
Communications systems can take different approaches to reducing spam and unwanted messages. In a social network, for example, ephemeral messages might be sent to users who have a relationship with the sender (such as friends). Not all social networking and messaging services offer the concept of friendship or relationships. A simple messaging service (SMS) or another contact-based messaging system may allow users to send messages to other recipients based on their phone number. These examples may not show a clear relationship between users.
A system that has defined relationships may limit spam communication by allowing users to only communicate with one another (or in a preferred format) if they have a relationship. A person might only be able to see the content-based messages of friends. In a communication system that doesn’t rely on a defined notion of friendship, this may not be possible.
Another problem with communication systems that offer ephemeral contents capabilities is that their interfaces can become messy and it may be hard to distinguish ephemeral messages from other types. Ephemeral content might be displayed in communications systems that allow users to post. Ephemeral content can also be displayed in messaging-based systems. Ephemeral information is used to communicate different types of information than messages or posts. Users who wish to view the ephemeral contents of their contacts might not want to go through a lot of messages or posts to find their ephemeral messages.
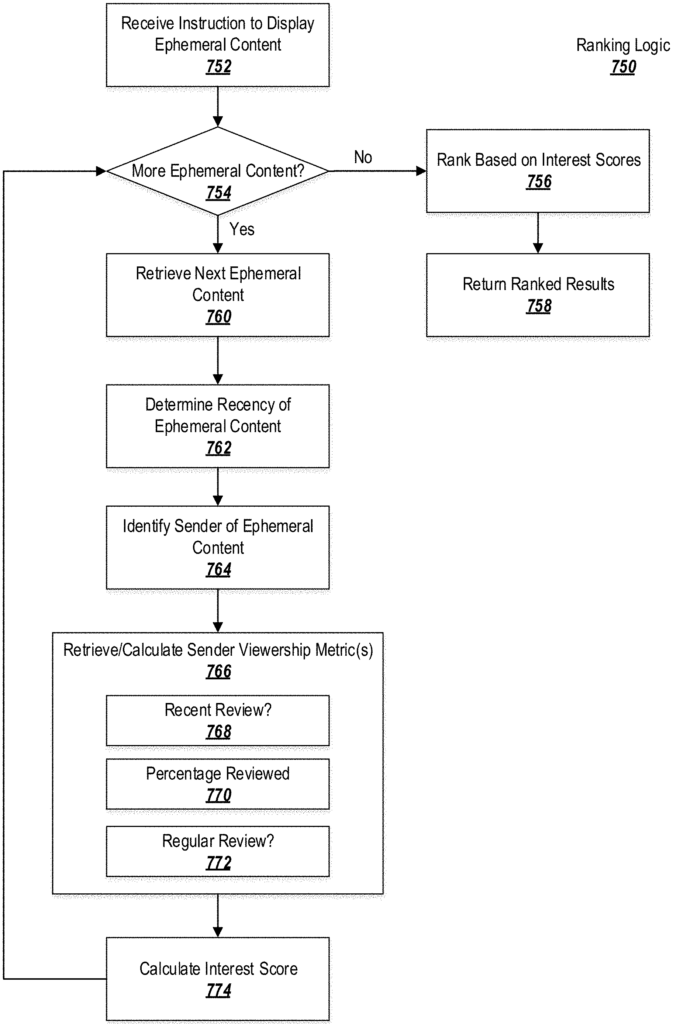
It is possible to display ephemeral contents in mixed messages by simply arranging them among the messages according to the order they were received. While chronological order may be appropriate for messages, users often have a greater interest in particular ephemeral contents than others (e.g. from close friends or family, rather than general acquaintances). A chorologically ordered ephemeral material may not be a useful way to display it.
Furthermore an ephemeral message can contain media (e.g. a picture or a video). It may be difficult for a recipient user to access the media while keeping encryption intact. Ephemeral messages can be sent to large numbers of people. Some ephemerality models may allow for the expiration of ephemeral contents at different times for different recipients. It can be challenging to make the ephemeral contents available to users who have not expired yet, but it may be impossible to make them unavailable to users who have expired.
Another issue that can arise in communications systems that provide ephemeral content is the problem of maintaining privacy for previously-transmitted ephemeral content. Users can perform operations to receive information about other users in some systems. One user might become friends with another user on a social networking site or follow that user to view their status. This is known as a “follow model”.
In a follow model the ephemeral information that a sender submits before being followed by another user might become visible to that user when the new recipient follows the sender. This means that ephemeral information sent before two users were connected could become visible to the new user after they are connected. This may not be desirable for some users who wish to keep their previous ephemeral contents private from new followers.
The follow model could also cause problems when it comes to preserving the end-to-end encryption for ephemeral messages. Many of the parameters used to encrypt ephemeral messages (e.g. message keys) are determined at the time the message is sent. This means that it might not be possible for strong encryption to continue if the message is later made accessible to new followers. To maintain encryption, it may be necessary to generate new encryption sessions post-hoc. This adds to the overhead of the communications network.
These and other issues can be addressed by exemplary embodiments that provide new techniques to send ephemeral messages to a communications or messaging system.
Streamlined entry points can be used to generate a message that includes content (such as ephemeral material) and for responding to messages containing ephemeral information previously sent. No matter what type of content or how it was generated, initial entry points are focused on a few clear use cases.
Two clear and simple use cases may provide initial entry to the ephemeral message functionality, regardless of how media was captured. The system might offer the option for the user to share media in an electronic content message or in a non-ephemeral message such as in a chat or conversation. The system solves the problem of identifying an appropriate entry point depending on the media type. As ephemeral media, many types of media are possible, including photos, GIFs, videos and weather reports.
To preserve end-to?end encryption, the ephemeral contents can be sent as a message. The following sections provide methods for sharing media with the message and encapsulating it as a message.
A user may reply to ephemeral material by replying. This could trigger a one-to-1 chat between the original user and the replying person. The privacy of the original sender is maintained. Ephemeral content can also be sent to a group, instead of being sent to all contacts. Replies may then be sent to the group. This embodiment preserves the privacy of the sender, as only the original group members to whom the message was sent are included in the conversation. The server can examine the membership of the group and verify that there is an encrypted session between members. This facilitates group communications.
Further embodiments” can be used in conjunction the embodiments above. They relate to methods for transmitting an electronic content message over a communications network.
Initially, the client sending the message may establish an encrypted session between possible recipients of the ephemeral contents (e.g., the user?s contacts list or a selected group). The first key may be provided during initial setup. The encrypted session is used by the client to send the message to the recipients. The encrypted content may include a thumbnail of the media item and a link to it. A second key is used to decrypt the media item.