Invented by Andrew J. Thomas, Karl Ackerman, James Douglas Bean, Kenneth D. Ray, Daniel Stutz, Sophos Ltd
The Sophos Ltd invention works as follows
Phishing attacks are designed to obtain valuable information from users, such as account credentials and personal information. They do this by posing a malicious inquiry as a legitimate request, usually in the form an email or other communication. Tracking outbound web traffic and electronic mail traffic inbound to an endpoint can improve detection of phishing or other attempts to obtain sensitive information.
Background for Tracking the use of corporate credentials
Enterprise networks can contain sensitive corporate and personal data that is increasingly attractive to malicious actors. In a commonly owned U.S. Patent Application Ser. No. No. 15/099 524 filed on April 14, 2016. 14, 2016, U.S. patent application Ser. No. No. 15/130.244 filed Apr. 15/130,244 filed on Apr. No. No. 22 2016, which are all hereby incorporated in their entirety by reference.
There is a continuing need for better techniques to detect and protect against malicious activities and their consequences.
Phishing attacks are designed to obtain valuable information from users, such as account credentials and personal information. They do this by posing a malicious inquiry as a legitimate request, usually in the form an email or other communication. Tracking outbound web traffic and electronic mail traffic inbound to an endpoint can improve detection of phishing or other attempts to obtain sensitive information.
The following figures will be used to describe the preferred embodiments. It should be noted that the foregoing can be embodied many different ways and is not limited to those illustrated in this document.
All documents referred to herein are hereby included by reference in full. Referring to singular items should also include plural items, unless the context makes it clear. Grammatical conjunctions can be used to express disjunctive or conjunctive combinations, such as conjoined sentences, clauses, words, etc., unless the context makes it clear. The term ‘or’ is used to express this. The term?or? “And so on.
The range of values referred to here is not meant to be restrictive, but rather refers to all values within that range. Unless otherwise stated, each value in the range is included as if they were individually listed. The words “about” and “approximately” are used. ?approximately,? When a numerical value is accompanied by a symbol or the like, it should be understood that the symbol indicates a deviation from the norm, as one would expect a person of ordinary skill to understand to achieve the intended result. The ranges of values or numeric values provided in this document are examples only and do not limit the scope of described embodiments. Use of all examples or exemplary language, (e.g. ?such as,? The examples (such as, or similar) are provided to help better understand the embodiments. They do not limit the scope of the claims or the embodiments. The specification does not include any language that would imply the existence of an unclaimed element essential to the practice or embodiments.
It is understood that the terms “first” and “second” are used in the description. ?second,? ?third,? ?above,? ?below,? Below,?
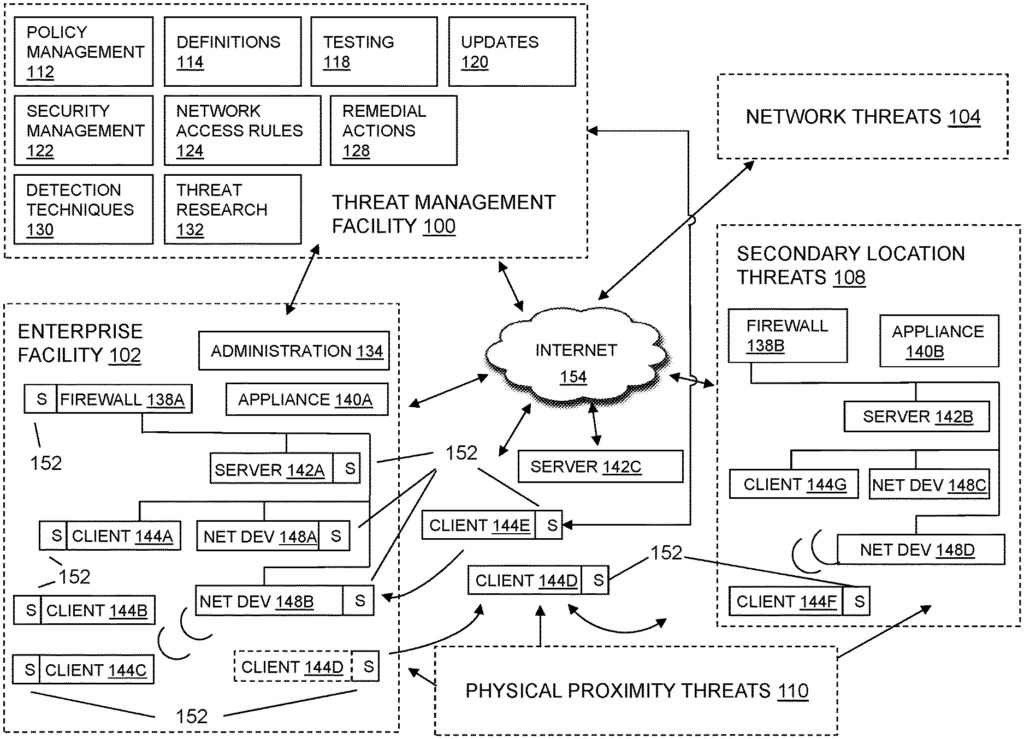
FIG. “FIG. Specifically, FIG. The block diagram in Figure 1 shows a system for threat management that protects an enterprise from a variety of threats. This is a context where the following techniques can be usefully deployed. A unified threat-management facility 100 is used to manage and implement corporate policies. A threat management facility 100 can be used, as will be explained below, to protect computer assets against many threats. These include both computer-generated and user-generated risks. Threat management facility 100 can be multi-dimensional, in that it is designed to protect corporate assets against a variety threats. It may also be adapted so it can learn about threats on one dimension. The threat management facility 100 may be multi-dimensional in that it can be designed to protect corporate assets from a variety of threats and it can also adaptable so as to learn about threats in one dimension (e.g. spam detection). The threat management facility is able to provide control capabilities for policy management. A corporation or another entity can institute a policy to prevent certain people (e.g. Employees, groups of employee, types of employee, guests of the corporation etc. Access to certain computer programs. The corporation can, for example, prevent the accounting department from accessing a certain version of an instant message service or even all services. The policy management facility 112 can be used in this case to update all corporate computing assets or only a few with the proper policy control facilities. The corporation can use the threat control facility 100 to set, update and control such policies. They only need to keep the threat control facility 100 updated on these policies. The threat management 100 can update all other corporate computing assets.
It should be understood that threat management facility 100 can provide multiple services. Policy management could be one of those services. Now we will describe some of the capabilities and components of threat management system 100.
In recent years, malware is a serious problem on the Internet. The importance of categorizing a threat as a virus, worm or other type is decreasing from both a technical and user perspective. No matter what the threat is, it may need to stop at different points in a networked computer environment, like an enterprise facility 102. This includes one or more laptops or desktops, gateways or communication ports, handhelds or mobile devices, or firewalls. It may also be of less value to the user to have different solutions for unknown and known threats. A consolidated threat-management facility 100 will need to use a similar set technologies and capabilities in order to protect against all threats. In some embodiments, a threat management facility 100 can provide a single desktop agent and scan any suspicious file. This method can eliminate the overlaps and gaps that are caused when viruses and spyware are treated as separate problems. It also simplifies administration and reduces desktop load. The level of connectivity for all IT users may have increased as the range and number of threats have grown. It is possible that this has led to an increase in the speed with which threats can move. A PC that is not protected and connected to the Internet 154 can be infected very quickly (possibly within 10 minutes), which could require a faster delivery of protection. The threat management facility 100 can update its anti-virus and spam product quickly and automatically, for example, every 5 minutes, every 1 minute, or continuously. The analysis and testing can be automated and performed more often. For example, they may complete the test in 15 minutes without compromising on quality. The threat management facility may extend techniques developed for malware and virus protection and make them available to enterprise facility 102 administrators in order to control their environments. The threat management facility 100 can also provide policy management to help control legitimate applications such as VoIP, instant message, peer-topeer file sharing, and similar ones that could undermine network performance and productivity within enterprise facility 102.
The threat management facility 100 can provide protection to an enterprise facility from computer-based malware such as viruses, spyware and adware. Trojans are also protected. FIG. In one embodiment, FIG. The block diagram 1 can show a threat management facility providing protection for an enterprise against multiple threats. Enterprise facility 102 can be corporate, educational, government, or other. The computer network of the enterprise facility may be spread across a number of locations and facilities. It may include a firewall (138A), an appliance (140A), server 142A and network devices (148A-B). Clients 144A to D, for example, may be protected by computer security facility 152. Any reference to client facilities can include the clients 144A – D shown in FIG. The same applies to FIG. 1 and vice versa. The threat management 100 may include multiple functions such as a security management facility, a policy management facility, an update facility, a definitions facility, e.g., a network access rules facility, redressal action facility, detecting techniques facility, testing facility, threat research facility, etc. The threat protection provided by threat management facility 100 can extend beyond the boundaries of the enterprise facility to clients 144D or client facilities that are not directly controlled or associated with the enterprise facility. Client facilities can be threatened by a variety of threats, including network threats 104 and physical proximity threats 110. Secondary location threats 108 are also possible. Clients 144A – D may be protected even when they are not physically located with the enterprise 102. For example, when clients 144E – F move in and out of enterprise facility 102. The threat management facility 100 can provide enterprise facility 102 with protection against a variety of threats affecting multiplatform computer resources across a number of locations and networks, using an integrated system approach. An enterprise model can be applied to any organization or user, regardless of size and type. An enterprise can be a group of users, endpoints or networks within or outside one or more protected areas. “An enterprise can include one or several offices, business locations or homes. Each location or portion of each location or a group of locations could be treated as client facilities.
In some embodiments, the Threat Management Facility 100 can be offered as a standalone solution. In some embodiments, the Threat Management Facility 100 can be integrated with a third party product. A programming interface for applications (e.g. Source code interfaces may be available to integrate the threat management facility. The threat management facility 100, for example, may be standalone in that it offers direct threat protection 100 to an enterprise, or computer resource. The threat management facility may also offer protection indirectly through a third party product. An enterprise can subscribe to services via the third-party products, and the threat protection provided to the enterprise by the threat facility 100 is through the third-party.
The security management facility may contain a number of elements which provide protection against malware for enterprise facility 102 computing resources. These include endpoint security, email security, web security, reputation-based filters, control over unauthorized users, guest computers and non-compliant machines, etc. Security management facility 122 can be a software program that provides malicious code and malicious applications protection for a computing resource in a client facility. Security management facility 122 can scan client facility files to detect malicious code. It may also remove or quarantine specific applications and files. Scanning the client facilities may include scanning all or some of the files on a regular basis, scanning applications when they are executed, scanning files while the files are being transmitted to or away from the client facilities, and the like. Scanners can scan files and applications to detect malicious code. In one embodiment, malicious code and unwanted programs may be continuously developed and distributed. Updates to the database of known codes may be provided periodically, on demand, as alerts, or in other ways.
The security management facility’s 122 email security and control may be able to help eliminate spam, viruses and spyware, as well as control email content. Email security and control provided by the security management facility 122 can protect against both inbound and outbound attacks, protect email infrastructures, prevent data leakage and provide spam filtering. In one embodiment, the security management facility may provide web security and controls, wherein security management can help detect or block unwanted applications, viruses, spyware and malware, as well as help control web browsing. This may enable safe and productive web browsing. Web security and control can provide Internet use policy, reporting on suspect device, security and content filters, active monitoring network traffic, URI-filtering, etc. In one embodiment, the security facility 122 can provide network access control that may allow control over network connections. Network control can prevent unauthorized systems, guests, or noncompliant systems, from accessing networks. It may also control network traffic, which cannot be bypassed at the client level. Network access control can also control virtual private networks. VPNs are a communications network that is tunneled by another network to create a logical link acting as a virtual connection. In some embodiments, a VPN can be treated the same way as a physical networking.
The Security Management Facility 122 can provide host intrusion protection through behavioral-based protection. This may guard against unknown attacks by analyzing the behavior before software code is executed. The behavioral based protection can monitor the code as it runs, and take action if the code appears to be malicious or suspicious. The advantages of behavioral protection over runtime security may include the ability to prevent code from running. While runtime protection will only stop code that is already partially executed, behavioral protection will identify malicious code on the gateway and file servers before it reaches endpoint computers.
The security management facility 122 can provide reputation filtering to identify or target known sources of malware. The threat management facility 100 may take immediate action if it detects URIs or IP addresses or domains that are known to be spam or sources of malware. “By dropping the source prior to any interaction, potential threats sources can be stopped before any data exchange can take place.
In embodiments of the invention, information can be sent back from the enterprise to a third-party, a vendor or the like. This may improve the performance of the facility 100 for threat management. The types, times and numbers of virus interactions a client has may be useful for preventing future virus threats. This feedback can be used for any aspect in threat detection. Information feedback may also be linked to behaviors of employees, including the most common policy violations, network accesses, unauthorized applications loading, unauthorized device usage, etc. This type of feedback information may allow for evaluation or profiling client actions that violate policy, which may provide a model to improve enterprise policies.
The security management facility may provide updates on malicious code to the enterprise facility network 102 and its associated client facilities. Updates may be planned, a reaction to a warning, a response to a request, a search for malicious code, etc. The administration facility can control the security management system 122 to perform updates. Updates may be transmitted automatically without the direct control of an administration facility 134 or manually by the administration facility. Security management facility 122 can manage malicious code description receipt from a provider. Distribution of malicious code description to enterprise facility networks 102, distribution to client facilities and so on.
The threat management facility 100 could provide a policy-management facility 112, which may be able block non-malicious apps, such as VoIP and instant messaging or peer-to-peer files sharing, that can undermine network performance and productivity within the enterprise facility. The policy management 112 can be a set rules or policies which indicate the enterprise facility 102’s access permissions to the client facility. This could include access permissions related to the network, external devices, applications and so on. The policy management 112 can include a text or database file, a combination text and databases, or other types of files. In an embodiment, a policy database may be a block list, a black list, an allowed list, a white list, or the like that may provide a list of enterprise facility 102 external network locations/applications that may or may not be accessed by the client facility. The policy management system 112 can include rules which are interpreted in relation to a network access request from enterprise facility 102 to determine whether the request should be granted. The rules could be a generic rule that determines the type of access which can be granted. These rules could be based on the policies for an enterprise facility 102’s client facility 102. There may be a policy that prohibits access to sporting websites. A security facility can access rules in a policy facility when a client facility requests a website. This will determine if it is related to sporting websites. In one embodiment, the security facilities may analyze the website requested to determine if it matches any of the rules within the policy facility.
The policy management facility 112 is similar to the enterprise facility 102 security management facility, but it includes enterprise facility wide access rules and polices that can be distributed in order to control client facility access. Policies may be defined by application type, subsets of application capabilities (organization hierarchy), computer facility type, type of user, network location and time, connection type or similar. The administration facility 134 may maintain policies, either through the threat-management facility 100 or in conjunction with a third party. A policy could, for example, restrict IM to support personnel only. It may be possible to allow instant messaging to departments that require it, while still maintaining network bandwidth to support other activities. The policy management facility 112 can be implemented in a number of ways. It may be a standalone application, incorporated into the network server facility 142, incorporated into the enterprise facility 102, incorporated within the client facility or similar.
The threat-management facility 100 can provide configuration management. This may be similar in nature to policy management but will examine and manage the configuration of operating systems, applications, hardware and other items. The assessment of a configuration can be done against a standard policy. It may also include detection of changes in configurations, remediation for improper configurations, or application of new configurations. A company may maintain a standard set of configuration rules and policies that may represent the desired status of the device. A client firewall, for example, may be installed and running, but disabled. The solution is to enable the firewall. Another example is that the enterprise could set a policy to disallow the use of USB drives and send a configuration change via registry to all clients.