APIs and integrations can be the hidden engine of a startup. They move data, trigger actions, connect products, and make a tool feel seamless to the user. On the surface, an API call can look simple. One request goes out. One response comes back. But the real value is often deeper than that. The value may live in how your system decides what to send, when to send it, how it maps one format to another, how it handles failure, how it protects access, or how it links many tools together in a way that saves time and creates a real business edge.
Find the Real Invention Behind the API
Most teams look at an API and see routes, payloads, auth, and docs. That is normal. Those are the visible parts. But a patent does not become strong just because it names the visible parts clearly.
A strong patent starts by finding the deeper thing that gives the API its value.
For a business, that usually means the part that saves time, reduces work, lowers risk, improves reliability, or makes customers stay because the product fits into their workflow in a way that is hard to replace.
Look past the endpoint and study the business result
A lot of founders begin in the wrong place. They start with the endpoint name, the request body, or the response format. Those details matter for product work, but they are rarely the heart of the invention.
The better move is to ask what happens for the user or customer because this API exists in the first place.
If the answer is that orders sync faster, compliance work gets easier, support tickets drop, or data can move across systems without manual cleanup, that is where the real claim thinking should begin.
When you frame the invention around a business result, you start seeing what needs protection. The real value may not be the call itself. It may be the way your system decides when to make the call.
It may be the way it merges data from systems that speak different formats.
It may be the way it blocks duplicate actions, catches bad data before it spreads, or keeps different tools in sync without breaking downstream workflows. That is where real claim value often lives.
Separate the wrapper from the engine
Many APIs are wrappers around deeper logic. The wrapper is how outside systems interact with your product. The engine is the hidden method that makes the output useful. Businesses should focus on protecting the engine.
This distinction matters because wrappers are easier for competitors to redesign. They can rename fields, move steps to a different service, or offer the same result through a different interface.
But if your claims capture the engine, the harder part to copy stays covered. A smart claim strategy does not chase surface detail. It aims at the mechanism that another company would have to rebuild to compete in the same way.
Ask what a copycat would need to reproduce
One of the best practical tests is to imagine a serious competitor trying to copy your customer value without copying your exact code. What must they still do? What steps can they not avoid?
What rules would they need to implement to get the same end result?
That exercise often exposes the real invention faster than any technical spec.
A company may be able to use different field names and a different API structure, yet still need the same sequence for validating input, mapping external objects into internal models, resolving conflicts, assigning actions, and confirming delivery across systems.
Those unavoidable pieces are often where your most useful claim language starts.
Find the point where technical design becomes business leverage
An API is not valuable just because it is technical. It becomes valuable when the design creates leverage for the business.
That leverage may show up as lower onboarding cost, better partner adoption, faster deployment, fewer human errors, or stronger retention because customers build workflows around your product.
When you draft around the real invention, you are really drafting around leverage.

That makes your patent more aligned with the actual growth of the company. It also makes your filing easier to defend internally because it ties the claims to product strategy, not just to engineering effort.
Do not confuse standard plumbing with patentable value
There is a lot of common plumbing in modern software. Authentication, rate limits, webhooks, pagination, retries, and token refresh are common parts of many systems.
By themselves, these may not be the strongest place to anchor your claims unless your approach changes how these pieces work together in a new way.
The strategic move is to find where ordinary technical blocks are arranged in a special way that creates a useful result. Businesses that win with APIs often do not invent every piece from scratch.
They combine known pieces in a way that removes friction others still live with. That arrangement can be the invention. The claim should then focus on that arrangement and what it achieves, not on generic parts in isolation.
Trace the full workflow, not just the call
The real invention often appears when you stop looking at a single request and start tracing the full workflow from trigger to outcome.
A single API call may look simple, but the full process may involve event detection, policy checks, data normalization, routing logic, downstream execution, failure handling, logging, and state updates across systems.
A business should map the whole flow in plain language. Describe what starts the process, what conditions change the path, what transformation happens to the data, what system takes the next action, and what final state is created.
That full path often reveals the exact technical method that makes the integration valuable and hard to replace.
Look for hidden decision logic
Many of the strongest inventions in APIs and integrations are not about moving data. They are about making decisions. The system may decide which system is the source of truth.
It may choose the next action based on user state, transaction type, system health, or prior events. It may decide whether to delay, merge, reject, enrich, or reformat data before passing it along.
That decision layer is easy to miss because teams often treat it as normal product logic. But from a patent angle, it can be the center of the invention.
If your system uses rules, thresholds, confidence scores, dependency checks, or context-aware routing to improve results, that logic deserves close attention.
It is often more defensible than the endpoint itself because it captures why the system behaves the way it does.
Pay attention to transformation, not just transmission
Some APIs mainly pass information through. Others transform information so it becomes useful in another context.
That transformation can be very valuable for businesses, especially when it reduces customer setup work or allows many external systems to connect to one internal model.
If your product converts messy outside data into a standard form, enriches records using internal context, resolves differences between data sources, or builds action-ready outputs from raw inputs, that is more than simple transmission.
It is a structured method for making integration work at scale. This is exactly the kind of operational intelligence that can support stronger claims.
The invention may live in timing
A surprising amount of API value comes from when something happens, not just what happens.
The order of operations, the timing of sync, the trigger conditions, and the way failures are handled over time can all shape the actual advantage.
For example, an integration may not be special because it syncs records. It may be special because it syncs only after a verification stage, then waits for a second event, then applies a conflict rule before updating a third system.
That timing sequence may prevent errors, reduce compute load, or avoid bad downstream effects. Businesses should not overlook sequence and timing when identifying the invention. Those details often define the practical edge.
Find what reduces customer pain
The strongest commercial inventions are often hidden inside removed pain. Think about what used to be hard before your API or integration existed. Maybe teams had to clean data by hand, build one-off scripts, chase failed syncs, or manually approve actions across different tools.
Maybe the problem was not visible to end users, but it cost the customer real time and money.
That removed pain is not just a sales point. It is often a clue to the inventive step. If your system takes a painful multi-step process and turns it into a reliable automated flow, the claim work should capture how that shift happens.
Businesses that connect patent drafting to customer pain usually end up with claims that protect something meaningful instead of something decorative.
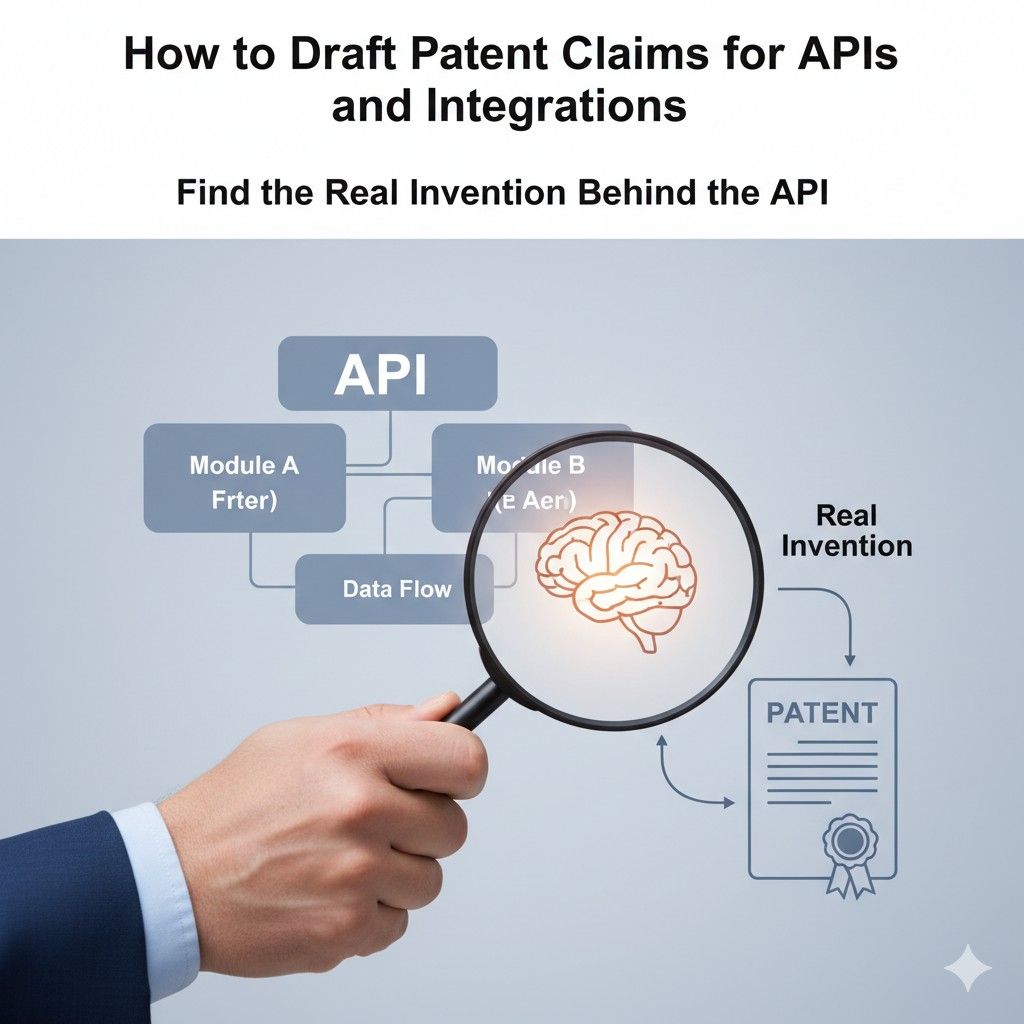
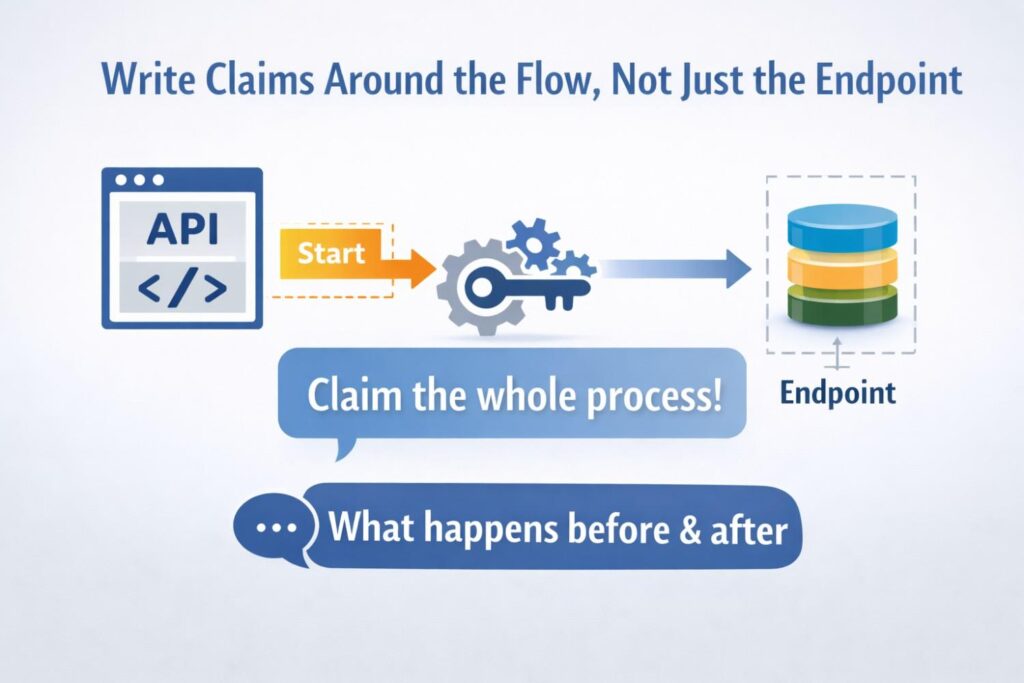
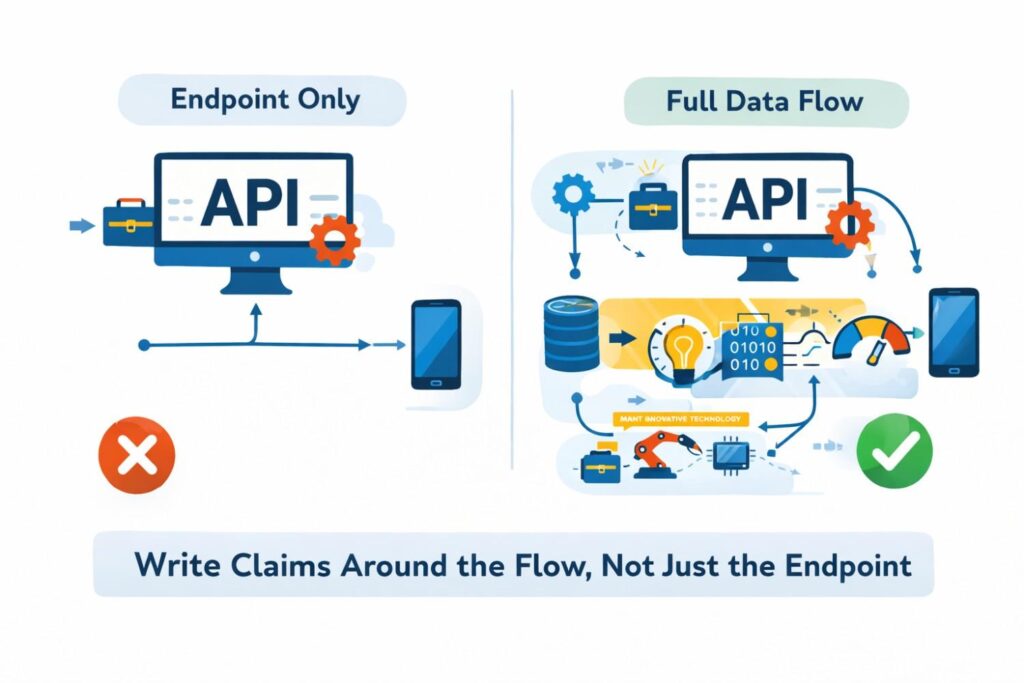
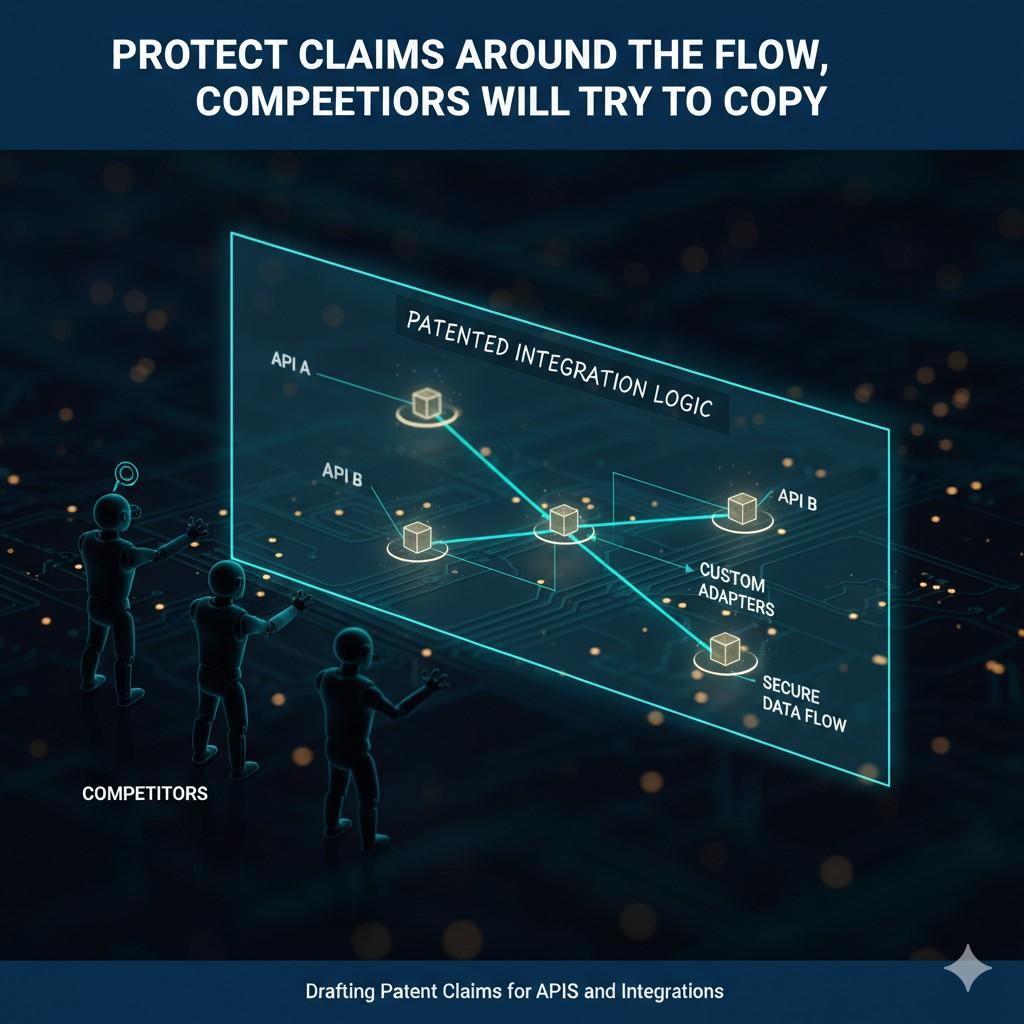
Write Claims Around the Flow, Not Just the Endpoint
Many teams make the same mistake when they try to protect an API invention. They write claims around the visible entry point.
They focus on the request, the response, and the endpoint name because those parts are easy to see and easy to describe. But that is usually not where the real value lives.
The stronger move is to claim the flow. The flow is the sequence of actions, checks, transformations, and outcomes that make the integration useful. That is the part a competitor often needs to copy to deliver the same result.
Why endpoint-focused claims break so easily
An endpoint is only one surface expression of a system. It is how one part of the world talks to another. It is not always the true engine of the result.
A competitor can often change the endpoint path, split one call into two calls, merge two calls into one, or move the logic behind a message queue, event bus, or background worker.
If your claims are locked too tightly to the endpoint itself, they may be easy to design around.
The endpoint is often just a door
A door matters, but it is not the whole building. In the same way, an endpoint may matter to the user or developer, but it is often only the first step in a larger chain.
The valuable part may be what happens after the request enters the system. That is where data gets verified, enriched, routed, synchronized, or transformed into an action that drives a real business outcome.
Surface detail is easy to swap out
Field names can change. Routes can change. Call structure can change. Even protocols can change over time.
A business that wants lasting protection should be careful not to tie the whole claim set to details that engineering teams routinely revise.
What tends to hold more value is the logic of the flow and the relationship between the steps.
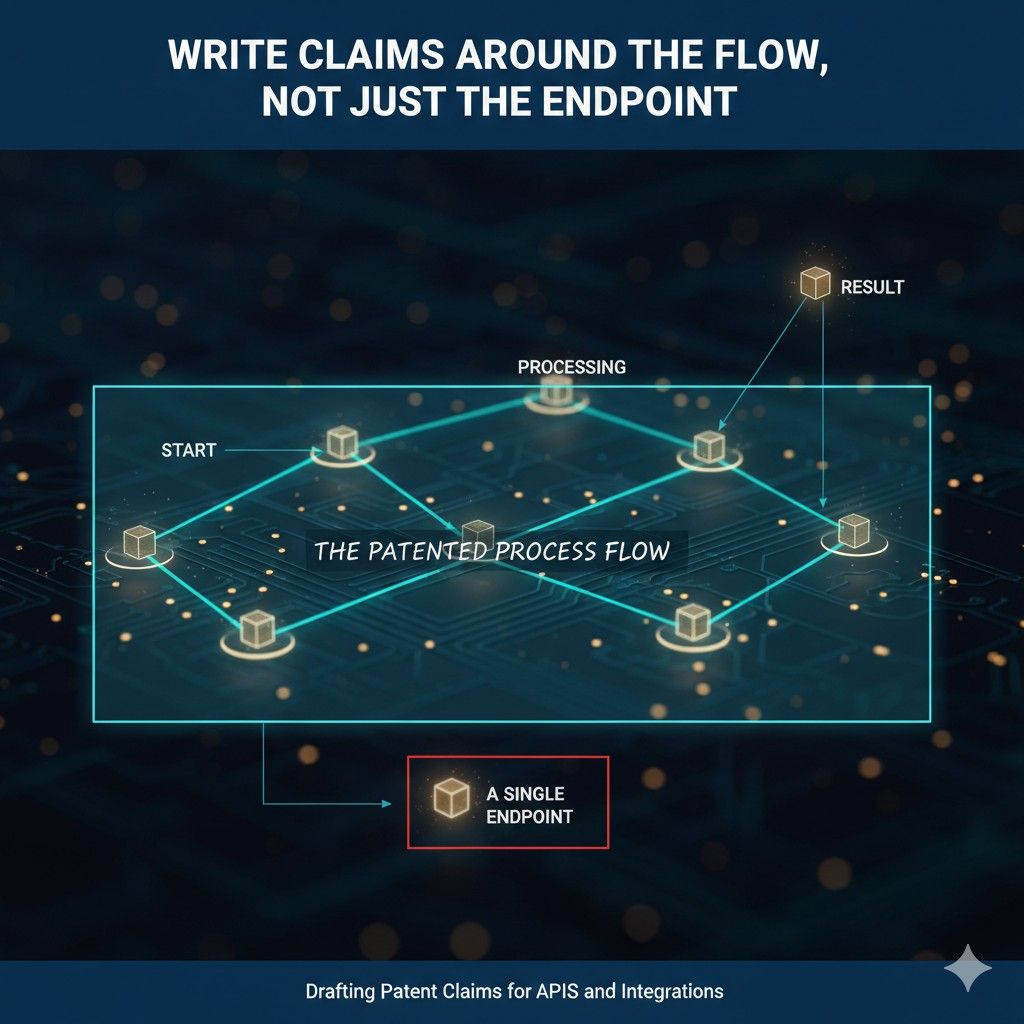
Start from the full journey of the data
The best claims often begin when you trace the full journey from trigger to outcome. Instead of asking what the endpoint accepts, ask what the system actually does from the moment an input appears to the moment a useful result is created.
That broader view reveals the mechanism that makes the integration worth protecting.
Trace the trigger
Every meaningful flow starts somewhere. It may begin with a request from an outside system, a change in internal state, a user action, a scheduled event, or a message from another service.
That trigger matters because it frames the first condition of the claimed method. If the flow begins under certain business conditions, that condition may be part of the invention.
Follow each state change
A useful way to sharpen claim thinking is to watch how the data changes state as it moves through the system. Maybe a raw event becomes a normalized object.
Maybe that object becomes a validated record. Maybe the validated record is matched against an internal model and converted into a downstream instruction. Each state change can reveal a step that matters.
End at the business outcome
The flow should not stop at technical completion alone. It should end where the value appears.
That may be a synchronized record, an automated task, a risk score, a triggered workflow, a permission-controlled action, or a confirmed update across multiple systems.
When you write around the full journey, the claims start to reflect commercial value instead of technical fragments.
A flow-based claim protects the method, not the label
This is the main strategic advantage. Flow-based claims are harder to escape because they target how the result is achieved. They are not limited to the outward label the product team happened to use.
That makes them more useful for real businesses that expect competitors to copy the concept but change the packaging.
Think in verbs, not product names
One of the best drafting habits is to step away from internal labels and move toward actions. Receive. Detect. Validate. Transform. Compare. Route. Generate. Transmit. Update. Confirm.
These verbs help you describe what the system is doing in a way that is less tied to current branding or architecture choices.
Focus on required relationships between steps
A flow is not just a group of actions. It is a set of actions in a meaningful relationship. One action may happen because a prior condition is satisfied. Another may happen only if a mismatch is detected.
Another may happen after a transformation creates a standard object. Those relationships are often where the invention really lives.
Claim the sequence that creates the advantage
Not every sequence matters. The important sequence is the one that creates the special result. That may be speed, trust, fewer failures, cleaner sync, or less setup work.
A business should identify the order of operations that directly causes the benefit users care about.
Order can be the whole difference
Sometimes two systems use the same parts but arrange them in a different order. That different order can change everything.
A system that validates before mapping may perform very differently from one that maps before validating.
A system that checks for conflict before writing to a downstream store may avoid duplicate actions that other tools create. That sequence can be the real inventive feature.
Timing matters as much as action
In many API-driven products, timing is part of the method. A process may wait for a second event, hold execution until a threshold is met, retry after a condition changes, or delay synchronization until a source of truth is confirmed.
These timing choices often create the reliability or efficiency that customers value. They should not be ignored in the claims.
Capture transformation steps with care
Many strong API and integration inventions are really about turning one thing into another in a useful way.
That transformation may be semantic, structural, contextual, or operational. If that is where the magic happens, the claims should make room for it.
Normalize outside data into an internal model
This is one of the most common and important examples. An outside system may send messy, incomplete, or differently structured data.
Your system may convert that input into a standard object that can be used across the platform. If that process is more than routine field copying, it may be central to the invention.
Enrich the input before action
Some systems do more than convert. They enrich. They may add internal history, account rules, prior events, usage signals, or policy checks before taking the next step.
That enrichment can turn a simple API exchange into a smart operational engine. For many businesses, this is where the defensible edge begins.
Generate a downstream instruction
In some products, the real value is that the system takes transformed data and creates a next action automatically.
It may open a ticket, update a CRM record, change access rights, trigger a workflow, or allocate system resources.
If the claim only covers receipt of the request and ignores the generated instruction, it may miss the most commercially important part.
Use conditions to define the real decision logic
A flow becomes more defensible when the claims reflect real decision points. These are the places where the system does not merely pass data through, but instead makes choices based on context.
That decision logic is often what separates basic plumbing from business-critical technology.
Conditional branching shows substance
If the system takes a first path when data matches a model and a second path when it does not, that branch may be important.
If a request is processed differently based on user status, system state, confidence score, source identity, or prior activity, those conditions can help show what makes the method useful and different.
Decision points are often harder to copy cleanly
A copycat may imitate the surface call quickly, but the deeper logic that decides when to merge, reject, split, defer, or trigger action is harder to reproduce without understanding the invention.
That is why businesses should spend time identifying these logic gates and not treat them as background detail.
Include failure handling where it creates value
Many real-world integrations become valuable not because they work in ideal conditions, but because they keep working when things go wrong.
Failure handling can be a major part of the method and should be considered carefully during claim drafting.
Real systems fail in messy ways
Requests time out. Source records arrive twice. Downstream systems reject updates. Permissions expire.
Data appears out of order. When your system handles these failures through a defined process that preserves consistency or avoids business harm, that process may be worth claiming.
Recovery logic can be inventive
A platform may retry only after a state check. It may isolate partial failures while allowing unaffected actions to continue.
It may generate a secondary object for reconciliation instead of pushing a bad update downstream. These are not just support details. They can be part of the core flow that makes the integration strong enough for enterprise use.
Keep the claim broad enough to survive implementation changes
This is one of the most practical lessons for founders and product teams. Your current implementation is only one version of the idea. The claims should be broad enough to protect the idea even as your system evolves.
Today’s architecture is not tomorrow’s architecture
You may use a REST endpoint today and event-driven processing tomorrow. You may move logic from one service to another. You may add asynchronous handling later.
A narrow claim tied to current deployment choices may lose value as your own product matures. A flow-based claim can stay useful across these changes because it protects the method, not just the shell.
Avoid locking onto unnecessary technical detail
One of the easiest ways to weaken a claim is to include details that are not essential to the value.
If a step can be performed in different ways and the result is still the same, consider whether the broader function matters more than the narrow implementation. This helps preserve room for both enforcement and future product growth.
Draft claims that mirror how buyers see the value
A patent may be technical, but the best claim strategy still connects to the reason customers buy.
Businesses should ask how the flow creates measurable value in the market and make sure the claims do not drift too far from that story.
Buyers care about outcomes
Most customers do not care that an endpoint exists. They care that the integration saves hours, reduces mistakes, speeds setup, keeps systems aligned, or allows automation across tools.
That means the protected flow should map to a practical result, not just to system structure.
Product advantage should show up in the method
If your product wins because it synchronizes records more reliably, routes work more intelligently, or lets partners connect much faster, the claim set should reflect the specific flow that creates that outcome.
That alignment helps the patent support the business instead of sitting apart from it.
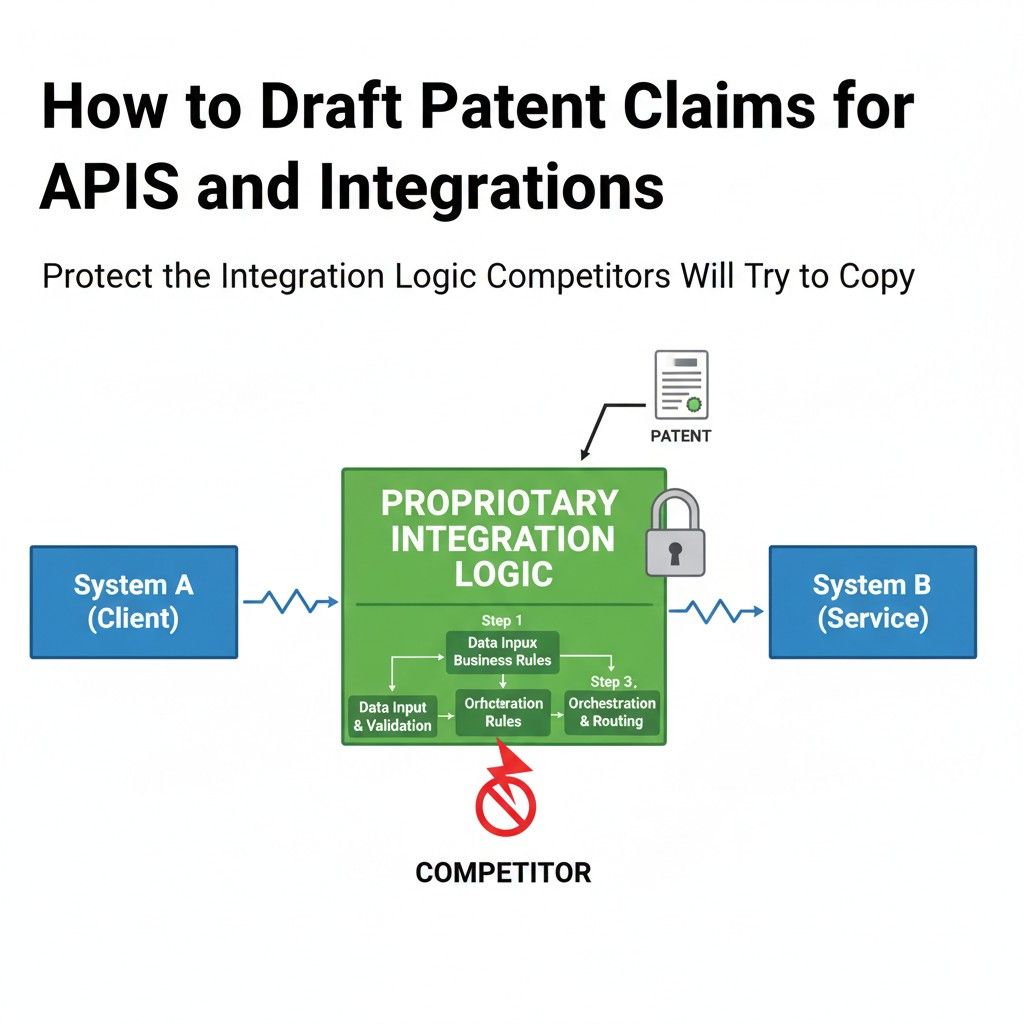
Protect the Integration Logic Competitors Will Try to Copy
The part most founders miss is often the part a competitor wants most.
It is usually not the endpoint name. It is not the payload shape by itself. It is not the public doc page. The real target is the integration logic that makes the system work in a way customers care about.
That logic is where your product becomes sticky. It is where manual work disappears. It is where systems stay in sync, actions happen at the right time, and users trust the result.
If you do not protect that layer, a competitor may copy the business value while changing just enough surface detail to look different.
The real risk is not cloning your interface
A lot of teams think about copying in a very literal way. They imagine a rival taking the same route names, the same request fields, and the same response format.
That can happen, but smart competitors usually do something more subtle. They study what your integration achieves, then rebuild the core logic with different labels and a different outer shell.
That is why claim strategy has to go deeper than the interface. Your protection should reach the logic that turns connected systems into a working product advantage.
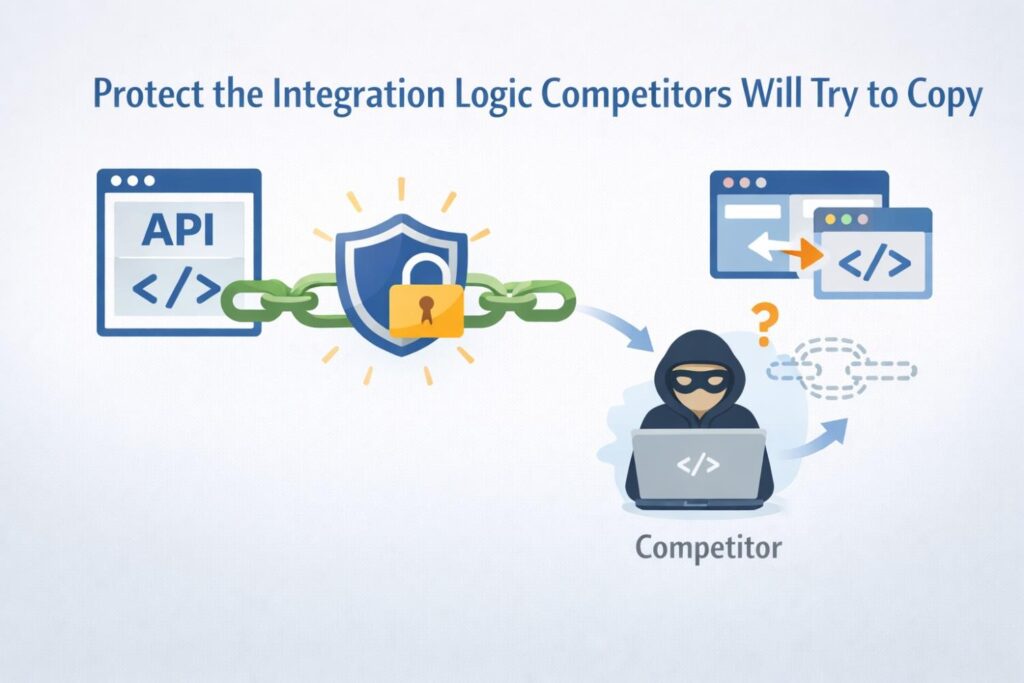
That is the layer that matters when buyers compare vendors, when partners decide what to build on, and when your platform becomes part of a customer’s daily workflow.
Integration logic is where business value gets locked in
For most software businesses, integrations are not side features anymore. They shape how fast customers launch, how much work gets automated, and how painful it would be to switch away later.
That means the logic inside those integrations can become one of the strongest parts of the moat.
What customers actually pay for
Customers rarely pay because an API exists. They pay because the integration solves an operational problem. It may reduce handoffs between teams. It may stop duplicate work.
It may prevent bad data from reaching other systems. It may allow one action in one tool to trigger the right outcome in another without human review. That is what creates business value.
When you look at your product through that lens, the logic becomes easier to spot. It is the rule set, process, and technical method that makes the operational result possible.
That is what competitors will study if they want to offer the same promise.
Why copied logic is more dangerous than copied features
A copied feature can be annoying. A copied logic layer is much more serious. That is because the logic layer often controls reliability, scale, and repeatable customer outcomes.
A competitor that recreates your key logic can narrow your advantage fast, even if their interface looks different.
This is especially true in markets where buyers care about workflow fit, automation, and system trust. In those markets, what matters is not whether two products look the same.
What matters is whether they produce the same useful result in the same kinds of environments.
Start by finding the decisions no competitor can avoid
The best place to focus is not on every technical detail. It is on the decisions a copycat would still need to make.
These are the moments in the integration where the system has to choose a path, assign meaning to data, resolve a mismatch, or trigger one action instead of another.
Decision logic often reveals the true moat
Many integration products look simple from the outside because the hard part happens invisibly.
The system may decide which incoming event matters, which source should control the final state, whether two records refer to the same thing, whether an update should be delayed, or whether an action should be blocked until another signal arrives.
That is not generic plumbing. That is operational intelligence. It is often the hardest part to design well, and it is often the main reason the integration performs better in production.
If a competitor wants your result, this is usually the logic they must recreate.
Focus on what stays constant across different implementations
A useful question for businesses is this: if a rival built the same value in a different technical stack, what logic would still remain? Maybe they would change the endpoint structure.
Maybe they would move from request-based calls to event-driven messaging. Maybe they would rename every object in the system.
But would they still need to validate a condition before syncing, normalize incoming records into a common model, compare against an internal source of truth, and then trigger a downstream action based on that comparison? If yes, that constant core is where strong protection begins.
Look at your integration where things go wrong
One of the clearest ways to find copy-worthy logic is to study the bad paths, not just the happy path. Simple systems work when nothing goes wrong. Valuable systems keep working when the world gets messy.
Reliability logic is often what makes the product enterprise-ready
In real environments, outside systems send incomplete data. Records arrive late. Events show up twice. Fields conflict. Access permissions change. Source systems drift from their expected format.
If your integration has a defined way to handle those situations and still protect the business outcome, that is highly meaningful.
A lot of founders overlook this because they see failure handling as basic engineering hygiene.
But in practice, this is often where the strongest know-how sits. A customer may choose your product because your sync does not break under stress.
A partner may trust your system because updates do not cascade into errors. That resilience may come from logic that is absolutely worth protecting.
Recovery methods can hold real patent value
A system may create a temporary record when conflict appears instead of overwriting the existing state. It may pause downstream action until a second confirmation arrives. It may route uncertain inputs into a review path while allowing high-confidence actions to continue.
It may reconcile partial failure without replaying the entire sequence. These are not throwaway details. They can define how your integration succeeds where weaker products fail.
Protect the mapping layer that makes systems understand each other
One of the most copied parts of an integration product is the layer that translates between systems.

This is where external formats, internal models, business rules, and downstream actions come together.
Mapping is often more than field matching
A weak view of mapping says it is just moving one field into another. A stronger and more realistic view is that mapping often includes interpreting meaning.
The system may need to decide whether a source object belongs to an existing record, whether a missing value should be inferred, whether multiple outside values should collapse into one internal state, or whether a source event should trigger one of several possible workflows.
That kind of mapping layer is strategic because it is tied directly to customer setup time and system usefulness. The easier and smarter that translation becomes, the faster the customer gets value.
A competitor will absolutely try to copy that if it drives adoption.
The best protection reaches beyond one schema
If your claims are too tied to one source format, they may miss the broader invention.
The stronger approach is to protect the method of transforming outside data into a usable internal representation based on certain rules, context, and outcomes.
That gives you a better chance of covering future versions and different implementations built on the same core idea.
Capture orchestration, not just connection
Some of the most valuable integration logic has nothing to do with simple connection. It has to do with orchestration. The system is not merely linking one app to another.
It is coordinating actions across multiple systems in a controlled sequence.
Orchestration creates high switching costs
When a platform becomes the place where many systems coordinate, it becomes much harder to replace.
The customer starts to depend not just on the connection, but on the ordering, conditions, checks, and automated actions that hold the workflow together. That orchestration layer often becomes a hidden but powerful part of the business moat.
If your product receives an event from one system, enriches it using internal state, checks policy against another system, creates a task in a third tool, and then updates a record in a fourth only after confirmation, that is more than integration. That is a protected method opportunity.
Sequence and dependency are often the hard parts
Competitors can build connectors. What is harder is rebuilding the exact dependency logic that makes those connectors useful. Which actions must happen first.
Which actions can happen in parallel. Which conditions block the next stage. Which outcomes trigger fallback behavior. These design choices are often the real substance of the product.
Wrapping It Up
Patent claims for APIs and integrations should not stop at the visible surface. The strongest protection comes from the real method underneath. That means the logic that decides what happens, the flow that moves data and actions across systems, and the rules that make the whole thing useful in the real world.
Leave a Reply